Ethical Hacking: Advantages and Disadvantages
Advertisement
This page explores the advantages and disadvantages of ethical hacking, along with its fundamentals.
What is Hacking?
Hacking is the process of identifying and exploiting potential entry points in a computer system or network. The goal is often to gain unauthorized access, with negative intentions like causing harm or stealing sensitive information.
Types of Hackers
There are primarily three types of hackers:
- White Hat Hacker: Also known as a security professional or security researcher. White hat hackers are employed by organizations to find vulnerabilities that malicious actors could exploit. They have permission to attack systems to identify weaknesses.
- Black Hat Hacker: Referred to as a “cracker” or simply the “bad guy.” Black hat hackers use their knowledge for malicious purposes.
- Gray Hat Hacker: A hybrid between white and black hat hackers. Their actions may sometimes be unauthorized but not necessarily malicious.
What is Ethical Hacking?
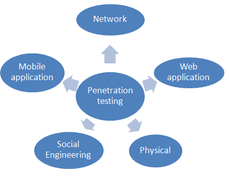
Ethical hacking involves performing penetration testing and identifying vulnerabilities to ensure the security of an organization’s information systems. Ethical hackers carry out the same activities as malicious hackers, but with the owner’s permission. They are typically employed by cybersecurity companies or organizations.
Goals of Ethical Hacking
The primary goals of ethical hacking are:
- Protecting systems from attackers.
- Ensuring the privacy of organizational data.
- Eliminating potential threats.

Ethical Hacking phases
Phases of Ethical Hacking
Ethical hackers typically follow these phases:
- Reconnaissance
- Foot-printing
- Scanning
- Gaining Access
- Maintaining Access
- Clearing Tracks
- Reporting
Importance of Ethical Hacking
Ethical hacking is crucial for:
- Providing security to important people or places.
- Protecting individuals and organizations from becoming victims of hacking.
- Securing common resources like banks and offices.
- Decreasing cyber attacks.
Advantages of Ethical Hacking
Here are the benefits of ethical hacking:
- Helps combat cyber terrorism and national security breaches.
- Enables proactive measures against potential attacks.
- Facilitates the development of systems resistant to penetration.
- Provides security to banking and financial institutions.
- Aids in identifying and closing vulnerabilities in computer systems and networks.
Disadvantages of Ethical Hacking
Here are the drawbacks of ethical hacking:
- Can potentially corrupt an organization’s files.
- Ethical hackers could misuse the information they gain. Trustworthy individuals are essential.
- Hiring ethical hacking professionals can be expensive.
- May pose risks to individual privacy.
- Potentially illegal depending on jurisdiction and scope of work.
Conclusion
Understanding the advantages and disadvantages of ethical hacking requires a grasp of its fundamental principles.
Advertisement
 RF
RF