WBAN Security Layer Basics: IEEE 802.15.6 Specifications
Advertisement
This page describes the IEEE 802.15.6 security layer basics for Wireless Body Area Networks (WBANs). It covers 802.15.6 WBAN security structures and explains the association and deassociation procedures.
The WBAN standard defines three levels of security based on security properties, protection levels, and frame formats:
- Unsecured communication level: Data are transmitted in unsecured frames. There are no mechanisms for data authentication, integrity, confidentiality, or privacy protection.
- Authentication level: Data frames are transmitted in a secured manner with authentication but without any encryption. This level does not support confidentiality or privacy.
- Authentication and Encryption: This level offers the highest level of security. Data frames are transmitted with both authentication and encryption.
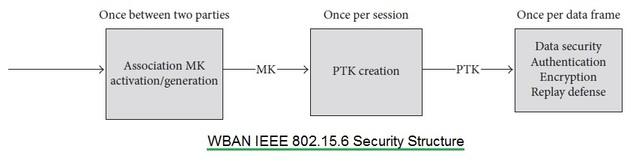
During the association procedure, one of the levels mentioned above is selected. A master key is then activated for secure unicast communication. This master key can be pre-shared or established using an unauthenticated association process. After this, a pairwise temporal key is created for a single session. For multicast secured communication, a group temporal key is shared among the corresponding group using the unicast method.
Figure 1 illustrates the process of activating the Master Key and establishing the Pairwise Temporal Key (PTK) for secured communication.
WBAN Security Association and Disassociation Procedure
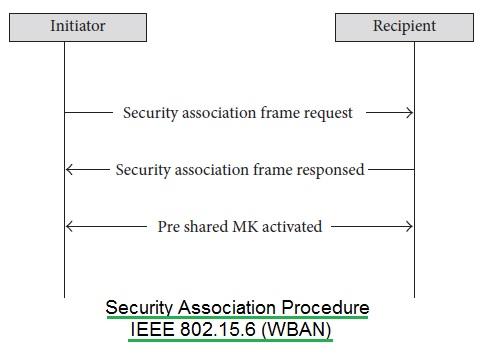
The private keys used in both association and disassociation procedures are independent and unique 256-bit integers.
Figure 2 shows the 802.15.6 WBAN association procedure:
- The node initiates the process by sending a security association frame request to the Hub.
- The Hub responds either allowing the node to join or aborting the request.
- If the node receives a response to abort, it stops the association procedure.
- If the node receives a joining response, the pre-shared master key is activated and shared between the node and the Hub based on mutual agreement. This key is used to generate a Pairwise Temporal Key (PTK).
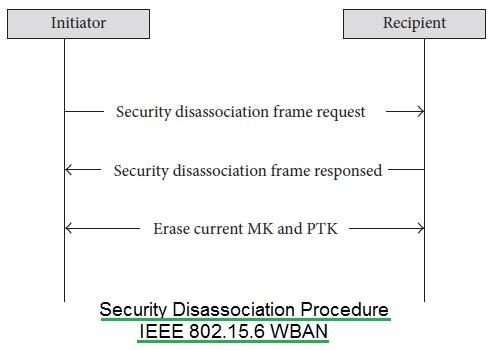
Figure 3 depicts the WBAN disassociation procedure. This can be initiated either by the node or by the hub.
As shown, the sender sends a security disassociation frame request and subsequently deletes the master key and the corresponding PTK from its storage. When the receiver receives the request, it also deletes the key information from its own storage.
Advertisement
 RF
RF








