GSM Burst Types: Roles and Structures
Advertisement
In the GSM (Global System for Mobile Communications) system, bursts are the structured data units transmitted during specific time slots on physical channels. A burst is a block of data with a defined format and timing, transmitted over the air interface. Different types of bursts exist in GSM, each serving specific purposes to ensure proper communication between mobile stations and base stations.
Let’s explore the main GSM burst types: Normal, Frequency Correction, Synchronization, and Access, including their roles and structures.
Normal Burst (NB)
The Normal Burst (NB) is the most common type of burst in GSM, used for carrying both voice and data during an ongoing call or data session. It’s designed for regular communication and the transmission of both traffic and control information.
Structure of a GSM Normal Burst:
- Total length of 156.25 bits.
- Two payload fields of 57 bits each, separated by a 26-bit midamble (used for equalization).
- A guard period of 8.25 bits at the end.
- 3-bit tail sequences at both ends (for error detection and correction).

Role of Normal Burst:
- Used for traffic channels (TCH) to transmit voice or data.
- Used for signaling information on dedicated control channels like SDCCH and SACCH.
- Contains the midamble, which helps the receiver in channel estimation and equalization to compensate for multipath fading.
- Facilitates continuous transmission during calls or data sessions.
Fields in each slot of a normal burst:
- Trail bits (TB): These are 3 bits at the beginning and end of each time slot, used for synchronization.
- Coded data: This encrypted data is placed in two 57-bit fields in each time slot.
- Stealing bit: It indicates to the decoder at the receiver whether the incoming burst is carrying signaling data or user data.
- Training sequence: Used for multipath equalization, this extracts the desired signal from unwanted reflections. This sequence also determines the channel the burst has traveled, aiding in correcting the rest of the frame and properly decoding the transmitted information.
- Guard bits: These are approximately 8.25 bits, used to avoid overlap of different bursts.
Frequency Correction Burst (FB)
The Frequency Correction Burst (FB) is used during network synchronization to help mobile devices tune to the correct frequency.
Structure of a GSM Frequency Correction Burst:
- Consists of 142 fixed bits of ‘0’ (zero sequence).
- No midamble, payload, or guard periods like the normal burst.

Roles of GSM FB:
- Broadcast on the Frequency Correction Channel (FCCH) to help mobile devices adjust their local oscillators to match the carrier frequency of the base station.
- Ensures that the mobile station is correctly tuned to the network’s frequency.
- Transmitted periodically by the base station to maintain frequency synchronization across all devices in the cell.
GSM FB is composed of the following fields:
- TB (3 bits) ; Fixed bit sequence (142 bits) ; TB (3 bits); Guard Time (8.25 bits)
Synchronization Burst (SB)
The Synchronization Burst (SB) provides mobile devices with timing information so they can synchronize with the base station’s time frame structure.
Structure:
- Consists of 78 bits of information (useful payload).
- A 64-bit training sequence, which includes the Base Station Identity Code (BSIC).
- Includes tail bits (3 bits at both ends) and a guard period (16.25 bits).
Roles:
- Broadcast on the Synchronization Channel (SCH) to help mobile devices synchronize their timing with the base station.
- Ensures that the mobile device is correctly aligned with the time slots used in GSM frames.
- Transmits the BSIC, which uniquely identifies the base station within a network, preventing interference with neighboring cells.
- Helps devices synchronize at the time slot level and frame level, essential for precise communication.
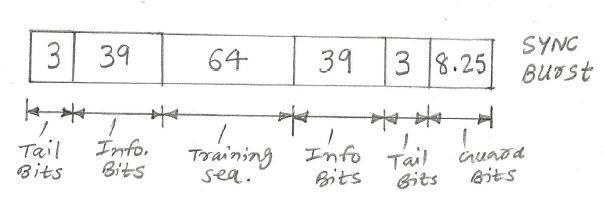
GSM SB is composed of the following fields:
- TB (3 bits) ; Coded Data (39 bits) ; Synchronization sequence (64 bits) ; Coded Data (39 bits) ; TB (3 bits) ; Guard Time (8.25 bits)
Dummy Burst (DB)
The Dummy Burst (DB) is used when there is no active data transmission over a time slot. Instead of leaving the time slot empty, a dummy burst is transmitted to maintain the integrity of the time-slot structure and avoid interference.
Structure:
- Similar to the normal burst, but the content is fixed, containing predefined data bits (like ‘1’s).

Roles:
- Transmitted in unused time slots on the Broadcast Control Channel (BCCH) or traffic channels (TCH) to maintain synchronization between the mobile station and the network.
- Prevents signal degradation and interference caused by empty time slots.
- Helps the network maintain the structure of the frame even when there is no active communication in that specific slot.
GSM dummy burst is composed of the following fields:
- TB (3 bits) ; Mixed (142 bits) ; TB (3 bits) ; Guard period (8.25 bits)
Access Burst (AB)
The Access Burst (AB) is specifically designed for random access procedures, where mobile devices request access to the network.
Structure:
- Shorter than the normal burst with a guard period of 68.25 bits to accommodate timing uncertainty, especially when the mobile station is far from the base station.
- Payload data consists of 41 bits (36-bit random access message + 5-bit tail bits).

Roles:
- Used on the Random Access Channel (RACH) by mobile stations to initiate a connection with the network, typically for making a call, sending an SMS, or performing location updates.
- The long guard period ensures that mobile devices can compensate for the propagation delay when sending access requests to the base station.
- Enables the network to detect mobile stations requesting service and allocate resources for further communication.
GSM access burst is composed of the following fields:
- Extended TB (8 bits) ; Synch sequence bits(41) ; Encrypted bits (36) ; TB (3 bits) ; Extended Guard period (68.25 bits)
Conclusion
Each type of GSM burst plays a critical role in the successful operation of the GSM network by facilitating communication, ensuring synchronization, and maintaining proper network management.
Advertisement
 RF
RF





