2G GSM Security: Authentication, Key Agreement, and Ciphering
Advertisement
Wireless security is designed to protect the integrity and confidentiality of mobile communications in a world where data security is critical. This guide delves into the various components of GSM (2G) security, such as authentication protocols, key agreement processes, message flow management, and the ciphering algorithms used to safeguard user data. By understanding these mechanisms, you can appreciate how GSM maintains secure communications for millions of users worldwide, defending against potential threats like eavesdropping and unauthorized access.
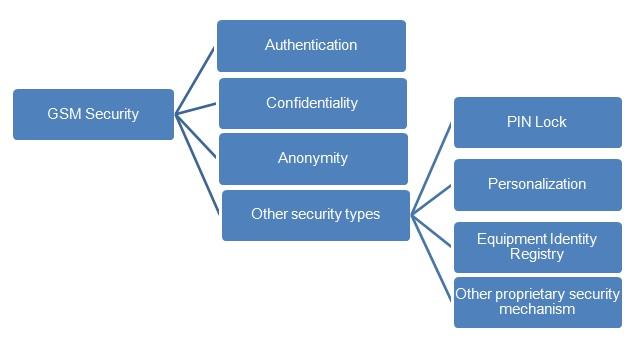
The GSM security mechanism is concerned with the following:
- Authentication (used for billing purposes)
- Confidentiality
- Anonymity (used to identify users)
- PIN Lock, EIR, personalization, etc.
Authentication Process
The authentication process helps the 2G network authenticate the correct user. This process is based on an exchanged secret key , which is known to the AuC (Authentication Center) and the SIM card. There is no provision to read the key from the SIM.
This authentication procedure in the GSM security mechanism is triggered due to the following:
- On the first access to the network
- Accessing the network for the purpose of making or receiving a call
- Location update process and the change of subscriber-related information stored in either HLR or VLR.
Anonymity
Here, the IMSI (International Mobile Subscriber Identity) is associated with a unique user (SIM). After the initial registration, a TMSI (Temporary Mobile Subscriber Identity) is assigned to the subscriber. The TMSI is stored along with the IMSI in the network HLR (Home Location Register).
GSM Authentication and Key Agreement

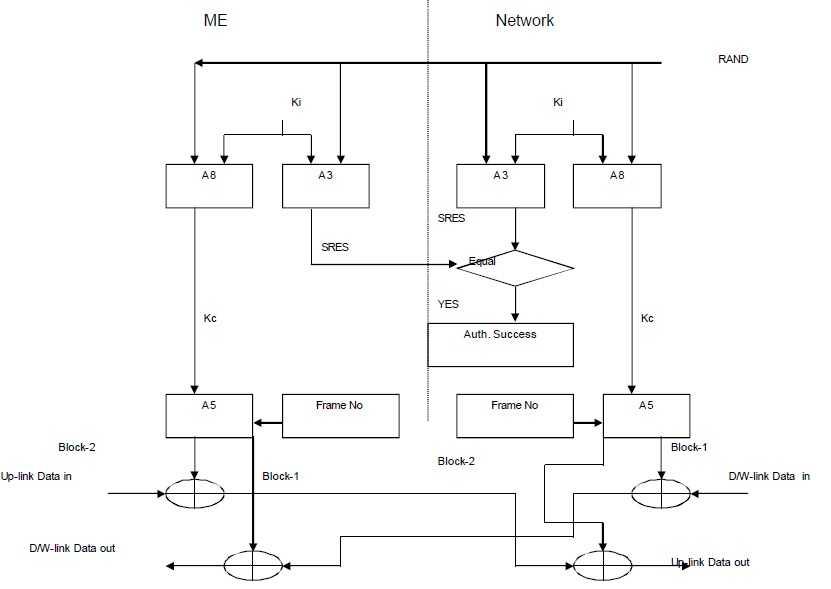
A3 and A8 keys are not made public. Triplets (RAND, SRES, Kc) needed to enable security are generated in the GSM mobile’s home Authentication Center (AuC).
Identity Confidentiality
The second important concept in GSM security is identity confidentiality. This protects the user from intrusion. This protection is provided to the GSM subscriber using TMSI (temporary mobile subscriber identity). TMSI can be provided to the GSM mobile either during the location update procedure (LAU) or during the TMSI reallocation procedure.
Message and Data Ciphering
In GSM, message and/or data ciphering is carried out using the A5 algorithm using the key .
PIN Lock and Personalization
The PIN lock is a feature by which the user can protect the usage of the SIM card by any unauthorized person. With personalization, the user can make the Mobile Equipment work only with his/her SIM card. Hence, the ME (Mobile Equipment) can be protected.
Message Flow During Authentication
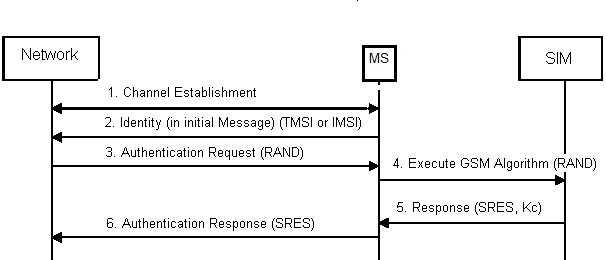
The mobile tracker feature developed by Samsung makes it possible to track the mobile when a SIM is inserted into any other mobile phone. As soon as a SIM is placed, the mobile equipment sends three messages to three pre-configured numbers. This helps track the stolen mobile with the SIM.
Once the user is authenticated, the RAND (delivered from the network) together with the (from the SIM) is sent through the A8 ciphering key generating algorithm to produce a ciphering key ( - 64-bits long). The A8 algorithm is also stored in the SIM card. The (generated by the A8 algorithm) is then used by the A5 ciphering algorithm to encipher or decipher the data.
The A5 algorithm is implemented in the hardware of the mobile phone, as it has to encrypt and decrypt data during the transmission and reception of information, which must be fast enough. The A5 algorithm takes the 64-bit long key and a 22-bit long representation of the TDMA frame number and produces two 114-bit long encryption words, BLOCK1 and BLOCK2, for use on the uplink and downlink, respectively. The encryption words are EXORed with the 114 data bits in each burst.
Ciphering Algorithms
Currently, there are three algorithms defined - A5/1, A5/2, and A5/3. A5/1 and A5/2 were the original algorithms defined by the GSM standard and are based on simple clock-controlled (linear feedback shift register) LFSRs. A5/2 was a deliberate weakening of the algorithm for certain export regions, where A5/1 is used in countries such as the USA, UK, and Australia. A5/3 was added in 2002 and is based on the open Kasumi algorithm defined by 3GPP.
Issues in Security Implementations in GSM
- Encryption terminates at the base station, and the rest of the GSM network entities are not covered.
- The length of (cipher key) is only 64 bits, which is inadequate.
- The GSM mobile cannot authenticate the network (BTS), but the reverse is possible.
- Integrity protection is not implemented.
- Ciphering algorithms are not available to the public and were managed only by GSMA.
Conclusion
GSM security plays a vital role in protecting mobile communications by employing a multi-layered approach that includes authentication, key agreement, and advanced ciphering algorithms. These security features work together to ensure that user identities are verified, data remains confidential, and communication channels are protected from potential breaches. With a solid understanding of these security mechanisms, you can gain insights into how GSM has established itself as a reliable and secure standard for mobile communication across the globe.
Advertisement
 RF
RF





