WLAN Security: Basics, WEP Protocol, and WiFi Checklist
Advertisement
This page covers WLAN security basics and the security methods used in Wireless LAN (WLAN) networks, also known as Wifi.
This wifi security describes security mechanisms, the WEP protocol, and the RC-4 encryption algorithm used in Wireless LAN (WLAN) networks. The figure below depicts the WLAN part integrated with LAN system components.
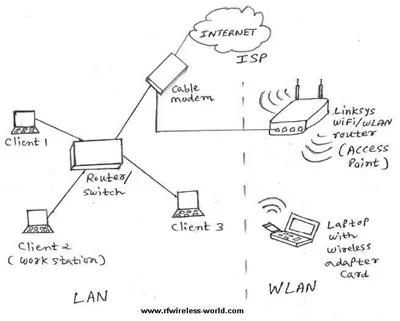
As shown, a WLAN system is composed of a Station and an Access Point. The Access Point helps interface wireless local area network devices with fixed LAN devices.
Wireless networks are more vulnerable to hacking compared to wired ones. Hence, more security is typically provided to the wireless portion. This wifi security is essential for wifi users accessing the wifi network at public places such as restaurants, airports, and railway stations.
WLAN has many benefits, such as user mobility, rapid installation, flexibility, and scalability.
WEP Protocol and Security Services
The WLAN security services are provided by the WEP protocol (Wired Equivalent Privacy protocol). This protocol protects link-level data during wireless transmissions between the stations (i.e., STAs/clients) and APs (Access Points).
WEP protocol takes care of security only in the wireless part and not in the wired part. There are three security services specified by IEEE for WLAN networks:
- Authentication: Denies access for stations who do not authenticate with the APs.
- Confidentiality: Prevents unauthorized entry into the WLAN network.
- Integrity: Ensures that messages in transit are not altered.
Authentication Types
There are two authentication types defined in WLAN systems (IEEE 802.11):
- Open System Authentication: Stations are allowed to join the WLAN network without any identity verification. It does not use any cryptography or encryption algorithm.
- Shared Key Authentication: Uses the RC4 cryptographic algorithm.
RC4 WLAN Security Algorithm
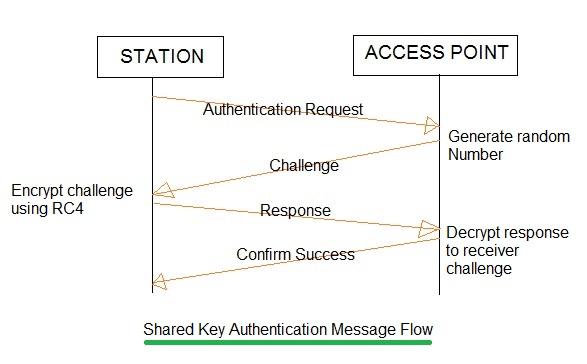
The following messages are exchanged between a Station (STA or Client) and an Access Point in shared key authentication:
- Authentication Request: From STA to AP
- Challenge: AP generates a random number and sends it to STA.
- Response: STA uses a cryptographic key (shared with AP) to encrypt the challenge and send it to the AP.
- Confirm Success: AP decrypts the result sent by the STA and allows access to the WLAN network, provided the decrypted value matches the random challenge transmitted initially.
WEP Protocol Explained
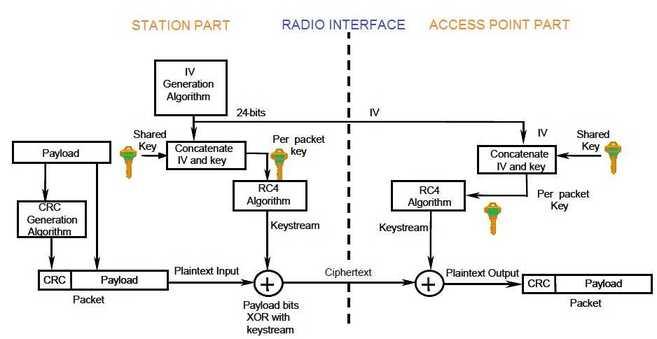
The WEP protocol is explained in the figure above. As shown, an Initialization Vector (IV) is added with a shared key to form the encryption key. The IV length is about 24 bits. The Encryption key length can vary from 40 bits to 104 bits.
For the 128-bit encryption algorithm, a 104-bit WEP key is used, which, when added to a 24-bit IV, becomes 128 bits in size.
This encryption key is then XORed with the payload information, which generates the ciphertext to be transmitted. Before modulo-2 operation, the payload data is appended with a CRC value of 32 bits, which aids in error detection.
WiFi Securities Checklist
The following is a WiFi securities checklist to protect the WLAN network or make the wifi network secured:
- Change the administrator password and username regularly.
- Turn WEP Encryption ON
- Enable firewall on each PC and router
- Disable the auto-connect feature
- Turn off the power of the router or AP when not in use
- Assign static IP addresses to the devices and keep them safe
- Disable broadcast of the SSID
- Enable MAC address filtering
Advertisement
 RF
RF





